Overview
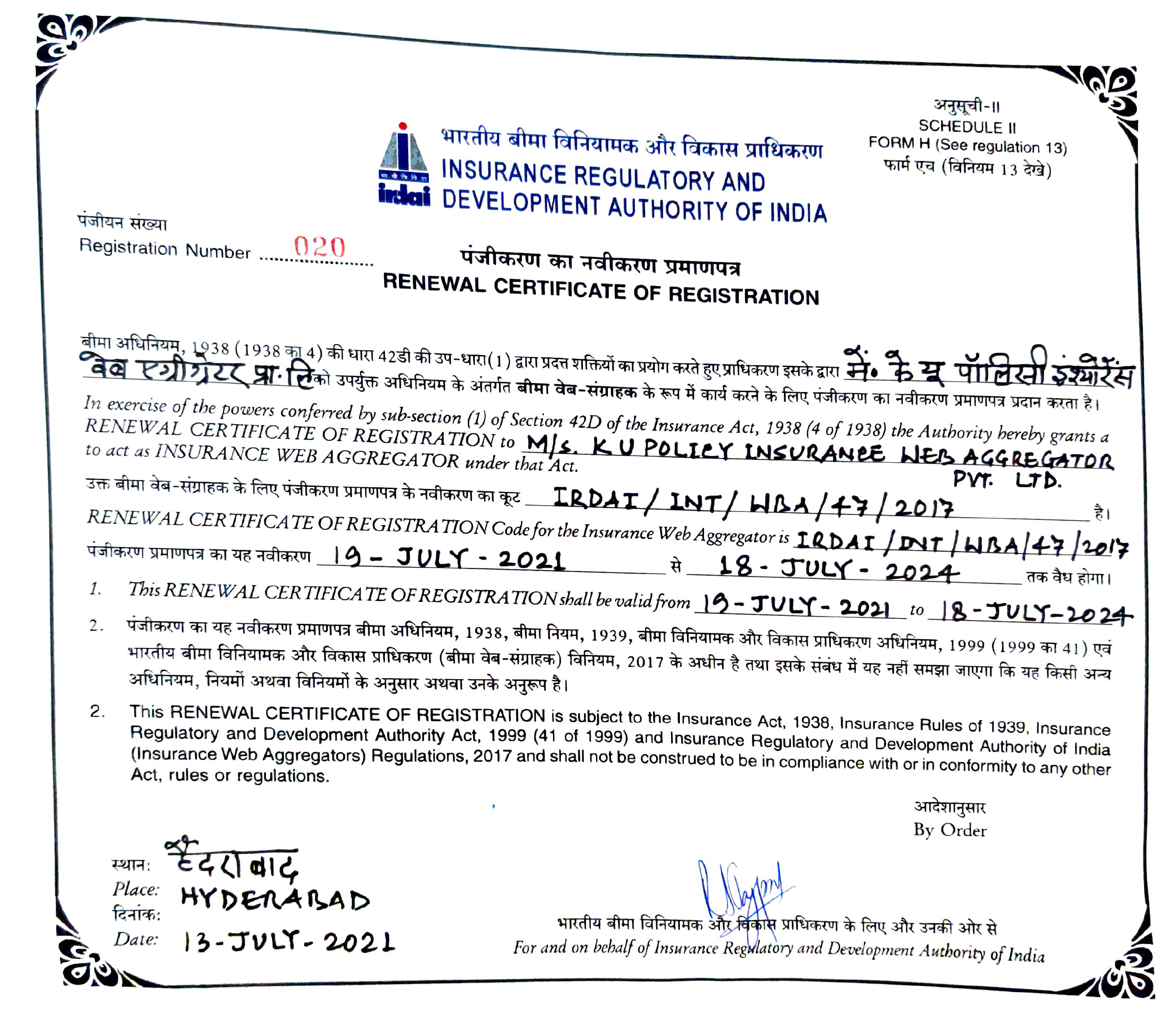
KU Policy Insurance Web Aggregator Private Limited., (hereafter, PolicyGhar) needs to gather, produce and use certain information that is confidential or private. The security of such information is important for PolicyGhar, as per industry standard and regulatory requirements. This policy describes how this confidential and private data must be collected, handled and stored to meet PolicyGhar data protection standards and to comply with the law.
Purpose
- PolicyGhar takes the privacy and security of all information including customers, employees, contractors, consultants, partners or other agents of PolicyGhar very seriously and has adopted security measures both within the physical environment in which all information is stored and within the applications to ensure that the customer's information is protected.
- Objective of the policy is to:
- To protect data / information that is confidential or private;
- To ensure effective procedures are in place to prevent loss of confidential and private information.
Scope
The policy applies to:
- PolicyGhar offices in all the locations.
- All employees of PolicyGhar.
- All contractors, suppliers and other people working on behalf of PolicyGhar.
Policy Review, Revision and Communication
This policy shall be reviewed and updated once every year to incorporate relevant changes. All subsequent updates to the policy shall be communicated over E-mail and made available on the intranet to all the employees by the end of March every year.
Policy
Roles and Responsibility
Following Roles and Responsibilities have been carried out in PolicyGhar:
Roles |
Responsibilities |
Board of Directors and Senior Management (Managing Partner and Partners) |
|
Information Security Group /Committee/ CISO |
|
Department Head |
|
Staff / Team |
|
Sensitive Personal Data
Sensitive personal data or information of a person means such personal information which consists of information related to:
- Password.
- Financial information such as bank account, credit card/ debit card or other payment instrument details.
- Physical, physiological and mental health condition.
- Sexual orientation.
- Medical records and history.
- Biometric information.
- Social Security / Unique Identification Numbers.
- Location Information.
- Political Affiliation.
Data Protection Principles
PolicyGhar will discharge its responsibilities in accordance with the requisite legal compliances (law of the land) and the following data protection principles contained therein:
- Obtain and process information fairly.
- Keep it only for one or more specified, explicit and lawful purposes.
- Use and disclose it only in ways as mentioned in this document.
- Keep it safe and secure.
- Keep it accurate, complete and up- to- date.
- Ensure it is adequate, relevant and not excessive.
- Retain for no longer than is necessary.
- Give a copy of personal data to the individual upon request.
Processing of Sensitive Data
Personal data of customers/ employees will be securely stored in electronic or manual form and in accordance with the requisite legal compliances (law of the land). In addition, data collected for a specific purpose, product or service may be stored at PolicyGhar with other information relating to an individual and only in accordance with the data protection principles mentioned above.
Data Transfer
PolicyGhar shall not disclose an individual's personal data outside their office except:
- When PolicyGhar has express consent to do so or in circumstances as agreed between PolicyGhar and an individual.
- When necessary to regulatory bodies and auditors.
- When PolicyGhar is required or permitted to do so by Law.
- To fraud prevention agencies where required.
Procedures and guidelines for Data Privacy>
- PolicyGhar shall maintain physical, technological and procedural safeguards and securities that comply with the requisite legal compliances (law of the land). PolicyGhar to ensure high standards in relation to data protection.
- Below are some of the steps that PolicyGhar shall take to ensure customers’/ employees’ data privacy:
- Access to sensitive data should be provided strictly on the basis of need to know;
- Backup should be kept in a safe and secure environment;
- Sensitive personal data should be shared with proper authorization as required;
- Data kept in file servers or shared servers should have proper access controls;
- Logs of the systems should be taken periodically and reviewed to identify the user access for the applications and servers containing sensitive personal data;
- Strict disciplinary actions should be taken if any breach of data protection standard is identified as per this policy;
- Data privacy should be ensured in using the company’s resources such as laptops, online applications, external storage devices, file servers, records and documents.
Data Migration
- Data migration plan shall include methods for verification of completeness, consistency, and integrity of migration activity, pre and post- migration activities along with responsibilities and timelines for completion of the same.
- The key aspects that are required to be consider must include:
- Integrity of data: indicating that the data is not altered manually or electronically by a person, program and substitution or overwriting in the new system. Integrity thus, includes error creep due to factors like transposition, transcription, etc.
- Completeness: ensuring that the total number of records from the source database is transferred to the new database (assuming the number of fields is the same).
- Confidentiality of data under conversion: ensuring that data is backed up before migration for future reference or any emergency that might arise out of the data migration process.
- Consistency of data: field/ record called from the new application should be consistent with that of the original application. This should enable consistency in repeatability of the testing exercise.
- Continuity: new application should be able to continue with newer records as an addition (or appendage) and help in ensuring seamless business continuity.
Procedures and Guidelines for Data Migration
- IT data migration activity must ensure the key aspects which are mentioned above.
- Explicit sign- offs from users/ application owners need to be obtained after each stage of migration and after the completion of migration process.
- Each migration phase must include documentation of audit trails, error logs, root cause analysis, etc. for easy recovery from migration failure.
Data Privacy Incident Management
Any incident of data privacy violation must be reported immediately to the group ID at admin@PolicyGhar.com.
Non- Compliance
Failure to comply with this policy may, at the full discretion of KU Policy Insurance Web Aggregator Private Limited., result in disciplinary action as per the policy.